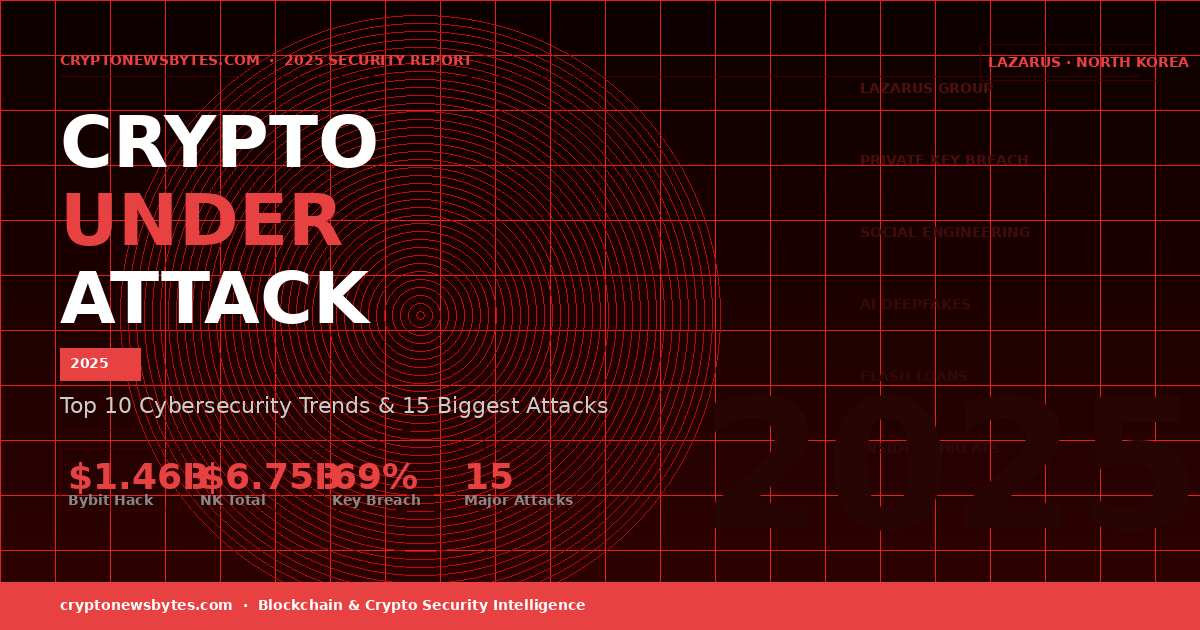
Top 10 Crypto Cybersecurity Trends 2025: The $1.46B Bybit Hack That Changed Everything
The top 10 crypto cybersecurity trends of 2025 tell a story of industrial-scale theft, compromised humans, and nation-state hackers operating with near-total impunity. It started with one developer’s laptop at a third-party vendor, and ended with $1.46 billion landing in the hands of North Korean operatives in a matter of minutes. The Bybit breach shattered every record in crypto security history and forced the industry to rethink what security actually means when the weakest link is a person, not a protocol. This is a full breakdown of the 10 most critical crypto cybersecurity trends 2025 produced, alongside the 15 largest confirmed attacks of the year ranked by losses.
2025
The Bybit hack of February 2025 ($1.46 billion stolen after a third-party developer’s laptop was compromised) remains the largest crypto security incident in history. Source: Chainalysis, CertiK, TRM Labs
- The Bybit hack on February 21, 2025 became the largest crypto theft in history. $1.46 billion was stolen after attackers compromised a single developer’s laptop at a third-party vendor called Safe
- North Korea’s Lazarus Group stole over $2 billion in 2025 alone, pushing total DPRK crypto theft since 2017 past $6.75 billion. The money funds nuclear weapons development
- Private key compromise drove 69% of all stolen value in H1 2025, with 158,000 documented cases affecting more than 80,000 unique victims
- CEX hot wallet breaches accounted for 88% of all Q1 2025 stolen amounts. Centralized exchanges are still the industry’s most dangerous single point of failure
- AI-generated deepfakes of Vitalik Buterin, Elon Musk, and CZ were used to promote fraudulent investment schemes throughout 2025
- The Coinbase insider bribery breach in May 2025 cost an estimated $400 million in remediation. No sophisticated hacking was involved, just bribing overseas subcontractors
- Venus Protocol in September 2025 became the year’s standout defensive success. AI monitoring flagged the attack 18 hours in advance, the attacker lost money, and all funds were recovered
- The Figure Technology breach on February 13, 2026 by ShinyHunters exposed 2.5GB of customer data through a single employee social engineering attack, part of a wider Okta SSO campaign
Across 2025, the crypto ecosystem lost over $2.2 billion to theft, exploits, and fraud. The crypto cybersecurity trends 2025 analysts had warned about arrived with full force: nation-state actors operated at industrial scale, AI-generated deepfakes impersonated the industry’s most trusted voices, and private key theft drove nearly 69% of all stolen value in H1 2025. Centralized exchanges proved to be the sector’s most dangerous concentration of risk, with private key breaches accounting for 88% of all Q1 stolen amounts.[1]
- $1.46B lost in the Bybit hack on Feb 21, 2025 (single largest crypto theft in history)
- $6.75B+ total stolen by North Korea’s DPRK since 2017
- 69% of all H1 2025 losses came from private key compromise
- 88% of Q1 2025 stolen value came from private key breaches at CEX hot wallets
- 158,000 phishing and malware cases documented in H1 2025, affecting 80,000+ unique victims
- $400M in remediation costs for the Coinbase insider bribery breach (May 2025)
- $0 stolen from Venus Protocol in September 2025 after AI monitoring caught the attack 18 hours early
Top 10 Crypto Cybersecurity Trends 2025: Full Breakdown
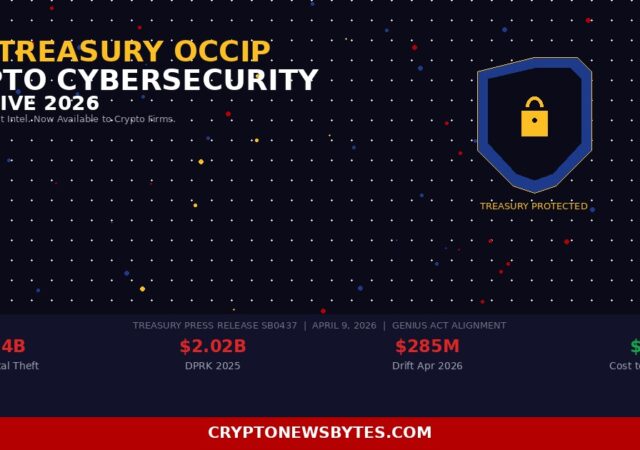
What was once a fringe concern about nation-state involvement in crypto theft is now confirmed reality. North Korea’s Lazarus Group stole over $2 billion in 2025 alone, pushing the regime’s total crypto theft since 2017 past $6.75 billion. The United States, South Korea, and Japan have all officially confirmed Lazarus’s role in major attacks including Bybit.[6]
What makes these actors so hard to stop is their patience. Lazarus operatives spend months building relationships, infiltrating vendor ecosystems, and staging attacks that exploit human trust rather than code vulnerabilities. The funds go directly to financing North Korea’s nuclear and ballistic missile programs, which means every Lazarus hack carries geopolitical consequences that extend well beyond the blockchain.
The Bybit hack did not begin at Bybit. It started at Safe, a respected wallet infrastructure provider, where attackers compromised a developer’s machine. When that developer’s code was later deployed into Bybit’s production environment, the attackers already had everything they needed to authorize a $1.46 billion transfer. The exchange itself was never directly breached.
This is the defining shift of 2025. The security perimeter is no longer the exchange itself. It is every vendor, contractor, and third-party developer the exchange relies on. Social engineering attacks targeting individual developers, customer support staff, and subcontractors became the dominant entry vector this year. Human trust is being exploited at scale, and no amount of code auditing catches it.
The private key is the single point of control over any crypto wallet. Lose it and you lose everything, with no recourse. In H1 2025, private key theft accounted for 69% of all stolen value, a figure that reflects both the scale of nation-state operations and a relentless epidemic of malware and phishing targeting everyday users. With 158,000 documented cases affecting over 80,000 unique victims, this is the form of crypto crime most users are most likely to personally encounter.[2]
Attack methods include information-stealing malware hidden in fake job offers (a Lazarus specialty), seed phrase phishing via lookalike websites, and clipboard hijacking tools that silently swap wallet addresses during transfers.
Centralized exchanges are crypto’s banks. They concentrate enormous pools of value inside infrastructure that, if breached, produces catastrophic and largely unrecoverable losses. In Q1 2025, private key breaches accounted for 88% of all stolen amounts, with the vast majority coming from CEX hot wallets. Hot wallets are internet-connected and designed to make withdrawals fast and seamless, which is exactly what users want and exactly what attackers exploit. In 2025, that convenience tradeoff cost the industry billions.[3]
The same instant liquidity that makes centralized exchanges appealing to everyday traders is what makes them the highest-value targets for nation-state hackers and organized criminal groups.
Generative AI handed attackers a powerful new toolkit in 2025. Deepfake videos of Vitalik Buterin, Elon Musk, and Binance founder CZ were deployed across social media to promote fraudulent investment schemes. The quality of these fakes improved dramatically over the year, making visual verification increasingly unreliable.
On top of that, AI-written phishing emails have become nearly impossible to distinguish from legitimate exchange communications. Perfect grammar, correct branding, and the right level of urgency. The Nigerian prince era of obvious scams is long gone. Today’s AI-generated phishing regularly fools security-aware professionals who know what to look for.
Cross-chain bridges are some of the most technically complex infrastructure in the entire crypto ecosystem, and also among the most frequently exploited. Because bridges have to coordinate logic across multiple blockchains at the same time, they create interaction surfaces that even the most thorough security audits can miss. In 2025, they remained high-value targets for exactly this reason. A single successful exploit can drain assets locked across multiple chains simultaneously, making the potential payoff enormous relative to the effort required.
Flash loan attacks exploit one of DeFi’s most unusual features: the ability to borrow enormous amounts of capital within a single transaction block, with no collateral required, as long as everything is repaid before the block closes. Attackers use this to temporarily manipulate price oracles and execute trades that would otherwise be impossible. The entire operation unfolds and resolves in one atomic transaction. The Abracadabra flash loan exploit in October 2025 extracted $1.8 million by finding a rounding error buried in smart contract logic. Small bugs, it turns out, can carry very large price tags.
The Coinbase breach of May 2025 required no sophisticated hacking at all. Attackers bribed overseas customer support subcontractors to hand over user data. That is it. No zero-day vulnerabilities, no advanced persistent threat tooling, just cash changing hands. The estimated cost of remediation and user compensation hit $400 million.[8]
Meanwhile, Figure Technology was compromised through a single social engineering attack targeting one employee, with the ShinyHunters group walking away with 2.5GB of customer data. The pattern is consistent across both cases. The crypto industry has invested heavily in smart contract security while leaving its human layer almost entirely undefended.
Stealing the funds is only half the problem. Converting billions in stolen crypto into usable currency without being traced is a complex operational challenge, and North Korea has solved it methodically. The regime runs a structured 45-day laundering pipeline: stolen ETH first moves through decentralized exchanges to break the tracing chain, then gets routed across bridges to different networks, sent through mixing services operating as Tornado Cash alternatives, funneled into Chinese-language OTC broker networks, and finally converted to fiat through peer-to-peer platforms. The permissionless, no-KYC nature of DeFi makes it nearly purpose-built for this kind of operation.
Not everything in 2025 went the attackers’ way. The Venus Protocol incident is the year’s clearest evidence that proactive security actually works. When Hexagate’s AI monitoring system picked up unusual patterns 18 hours before a planned attack on BNB Chain, the protocol had time to act. When the attacker finally executed, the exploit failed completely and they lost money in the process.[9]
Across the industry, on-chain governance mechanisms that let token holders vote to freeze compromised assets are beginning to emerge as a legitimate defensive layer. If widely adopted, they could meaningfully change the risk calculation for attackers targeting DeFi protocols.
Top 15 Biggest Crypto Attacks of 2025
The following table ranks the 15 largest confirmed crypto security incidents of 2025 by estimated losses. Data sourced from Chainalysis[1], CertiK[2], Beosin[3], TRM Labs[4], and DeFiLlama[5].
| # | Protocol / Platform | Date | Attack Type | Est. Loss | Chain(s) | Recovery | Attribution |
|---|---|---|---|---|---|---|---|
| 1 | Bybit | Feb 21, 2025 | Social Engineering + Private Key | $1.46B | Ethereum | Minimal (<5%) | North Korea · Lazarus |
| 2 | Cetus Protocol | May 22, 2025 | Smart Contract Logic / Spoof Token | ~$223M | Sui | ~$162M Recovered | Unknown |
| 3 | Balancer Protocol | 2025 | Smart Contract Exploit | ~$128M | Ethereum | Partially Traced | Unknown |
| 4 | Nobitex (Iran) | Jun 18, 2025 | Hot Wallet Compromise | $80–90M | Multi-chain | Unknown | Pro-Israeli Hacktivists |
| 5 | Phemex | Jan 2025 | Hot Wallet Compromise (16 chains) | >$73M | Multi-chain | Minimal | North Korea · Lazarus |
| 6 | UPCX Protocol | Apr 2025 | Private Key Compromise | ~$70M | Multi-chain | Unknown | Unknown |
| 7 | Coinbase | May 2025 | Insider Bribery / Social Engineering | $400M remediation | Off-chain | Data only — no funds | Criminal Organization |
| 8 | BtcTurk (2nd incident) | Aug 14, 2025 | Hot Wallet Key Compromise | >$48M | Multi-chain | Some frozen (Binance) | Unknown |
| 9 | Upbit | Nov 2025 | Solana Hot Wallet Compromise | ~$36M | Solana | $1.77M Frozen | North Korea · Lazarus |
| 10 | Figure Technology | Feb 13, 2026 | Social Engineering → Data Breach | 2.5GB data stolen | Off-chain | No funds — data breach | ShinyHunters |
| 11 | IoTeX (IOTX Safe) | 2025 | Smart Contract / Safe Exploit | ~$10M+ | IoTeX | Unknown | Unknown |
| 12 | WEMIX Gaming | Feb 2025 | Authentication Key Theft | ~$6.1M | WEMIX | Criminal complaint filed | Unknown |
| 13 | AdsPower Supply Chain | Jan 21–24, 2025 | Plugin Supply Chain Attack | ~$4.7M | Multi-chain | Unknown | Unknown |
| 14 | Abracadabra | Oct 1, 2025 | Flash Loan / Rounding Exploit | ~$1.8M | Ethereum | ~33% Recovered | Unknown |
| 15 | Venus Protocol ✓ | Sep 2025 | Oracle / Smart Contract (Blocked) | $0 stolen ✓ | BNB Chain | Fully Recovered | Attacker lost money |
* The Venus Protocol entry is notable as 2025’s standout defensive success. Real-time monitoring by Hexagate provided 18 hours of advance warning, enabling full fund recovery and causing the attacker to actually lose money.[9]
How to Protect Your Crypto in 2026
Most of what is described above targets exchanges and protocols, not individual users directly. But private key theft and phishing affect everyday holders constantly. The good news is that most individual-level attacks are entirely preventable with a few consistent habits.
For significant holdings, move funds off exchanges entirely. Hardware wallets keep your private key offline and inaccessible to remote attackers.
No legitimate exchange or support team will ever ask for your seed phrase. Any request for it, from any source, in any format, is a confirmed attack.
If a video of a public figure is promoting a crypto giveaway or wallet connection, it is fake. Always verify through the person’s official verified accounts before acting on anything.
Bookmark every exchange and DeFi platform you use directly. Never click email links. Check every character in a URL before connecting your wallet.
Keep only what you’re actively trading on centralized exchanges. Hot wallets at major exchanges are the industry’s most targeted asset.
Use tools like Etherscan alerts, Zapper, or DeBank to get real-time notifications of unexpected transactions from your wallet addresses.
What to Watch For in the Months Ahead
The crypto cybersecurity trends 2025 produced will shape what attackers do next well into 2026 and beyond. Lazarus Group is not slowing down. With over $2 billion secured in 2025 alone, the group now has significant resources to fund even more sophisticated multi-stage operations against institutional-grade targets. Exchanges, custodians, and the third-party vendors they depend on should expect continued, sustained pressure.
The AI arms race between attackers and defenders is still in its early stages. Deepfake quality is improving faster than detection tools can keep up with. Phishing attacks will become more personalized as attackers use publicly available data to build highly convincing impersonations at scale. On the regulatory front, the Bybit and Coinbase incidents have given regulators clear justification to push harder for mandatory standards around hot wallet exposure limits, key management practices, and third-party vendor auditing requirements in the US, EU, and across Asia.
On the defensive side, Venus Protocol proved that AI-powered real-time monitoring is no longer theoretical. It works, and it saved every dollar in that protocol. The wider adoption of on-chain monitoring services and governance-based freeze mechanisms as standard security infrastructure is now a realistic expectation rather than a distant aspiration.
Sources & Citations
- [1] Chainalysis Crypto Crime Report 2025 — chainalysis.com
- [2] CertiK Hack3d Q1 2025 Security Report — certik.com
- [3] Beosin Web3 Security Report H1 2025 — beosin.com
- [4] TRM Labs Crypto Crime Annual Report 2025 — trmlabs.com
- [5] DeFiLlama Hacks Tracker — defillama.com/hacks
- [6] FBI Advisory — North Korea Cyber Actors / TraderTraitor (Bybit Attribution) — fbi.gov
- [7] Bybit CEO Official Statement — Bybit Blog, February 2025 — blog.bybit.com
- [8] Coinbase SEC Filing — Data Breach Disclosure, May 2025 — investor.coinbase.com
- [9] Hexagate Security Report — Venus Protocol Incident, September 2025 — hexagate.com
- [10] CryptoNewsBytes Security Coverage — cryptonewsbytes.com