By Anujith
Blockchain is a technology where a network of computers maintain a shared, verifiable, and permanent record of data. It is a distributed database comprised of two or more block records (referred to as “blocks”), which are linked together while adhering to a predetermined standard or protocol. Each node in a blockchain can be considered as a ledger, hence blockchain is also referred to as “Distributed Ledger Technology” (DLT). Essentially, it is built on 3 underlying technologies: private key cryptography, P2P (peer-to-peer) network, and the protocol program.
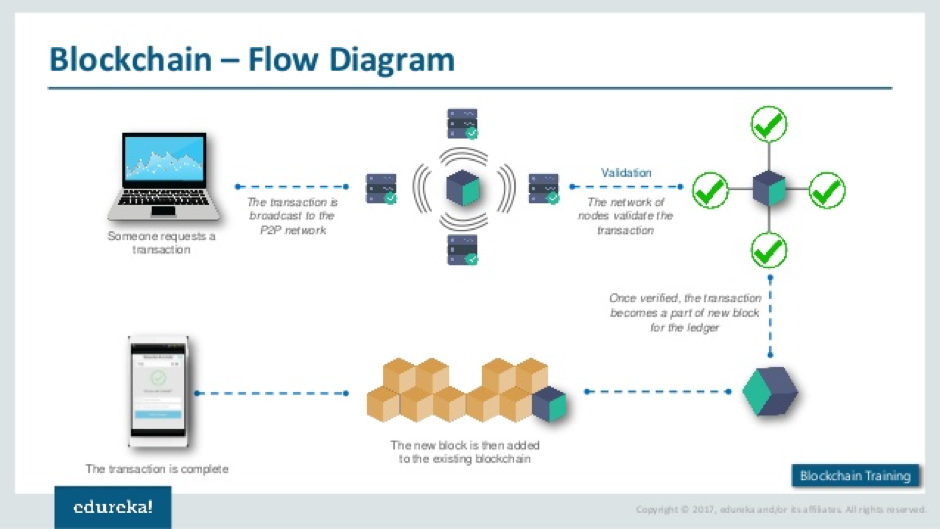
Image source: Edureka blockchain training
Unlike systems where there is one centralized server or other mode of ensuring that every update goes through one central point of authority, in case of blockchain every node has the same authority, and same version of information. Each node has the chance to update the blockchain independently. The most popular record becomes to de-facto official record.
Each block in a blockchain is a data structure, which contains link to the previous block in the chain, a payload (the relevant transaction data), the hash value (a randomly generated and unique sequence of numbers and letters, serving as the unique secret identifier), and a proof of work (POW).
A combination of user, software and specialized hardware, commonly referred to as “Miner”, can update the blockchain. The term mining is very widely used in the context of Bitcoin, which is an application of the blockchain technology, however, the concept is the same all over blockchain.
Changing or deleting existing blocks is not possible, hence, to update a blockchain, a new block has to be created. To create a new block, each miner has to provide proof of work (POW) for the last recorded block in the blockchain, an operation which is essentially massive number-crunching, done at high speed. This is in an environment where many other miners are also doing the same, which makes it more difficult for any miner to provide POW. This makes updating blockchain very hard, only when proof of very significant number-crunching work done is provided, a miner gets to create a new block. Hacking blockchain is, hence, a very hard thing to do.
As you can see above, it is not one particular administrator providing the credentials for the others to trust the data. Rather, in this system, a large number of participating nodes create data blocks using cryptography method. It’s the POW provided by the miner that determines whether that miner would be able to create a new block. Hence, every block in a blockchain is mathematically verified information, and data integrity can’t be breached. This is why blockchain is considered a “trustless” system.
Why do miners use special software and hardware? When updating a blockchain, i.e. creating a block, the miners essentially first create a “hash”. A hash is a seemingly random sequence of letters and numbers, which encapsulates the information in the block. The hash is stored along with the block, at the end of the blockchain. It is not the just the transaction data for the new block that is used, to create the hash. The hash for the last block in the blockchain is also needed. This is what makes the processing of mining a very large and resource-intensive number-crunching operation. The “hash rate” is the speed with which the computer does this massive number-crunching. A miner has more chances of updating the blockchain if his/her hash rate is high. This is the reason the miners use specially designed high-performance software and hardware.




