- A new macOS malware named “KandyKorn” linked to the North Korean hacking group Lazarus has targeted blockchain engineers of a cryptocurrency exchange platform.
- KandyKorn utilizes social engineering techniques through Discord channels, distributing a malicious ZIP archive disguised as an arbitrage bot, to steal and manipulate information.
- The presence of KandyKorn highlights Lazarus’ ability to create sophisticated and inconspicuous malware for Apple computers, emphasizing the importance of strong cybersecurity measures in the cryptocurrency sector.
In the ever-evolving realm of cybersecurity, a new malware has emerged, casting a shadow of concern over Apple’s macOS. This sophisticated malware, known as “KandyKorn,” has been linked to the notorious North Korean hacking group Lazarus. Specifically, it has set its sights on blockchain engineers associated with a prominent cryptocurrency exchange platform. In this article, we delve into the intricacies of KandyKorn, its modus operandi, and the implications it poses to the cryptocurrency community.
Unmasking KandyKorn: A Stealthy Threat
An in-depth analysis conducted by Elastic Security Labs has shed light on the capabilities of the macOS malware, KandyKorn. This insidious backdoor possesses a range of malicious features, including data retrieval, directory listing, file upload/download, secure deletion, process termination, and command execution. Its stealthy nature allows it to infiltrate users’ computers without raising immediate suspicion, making it a potent tool in the hands of cybercriminals.
The Path of Infection: Discord Channels and Social Engineering
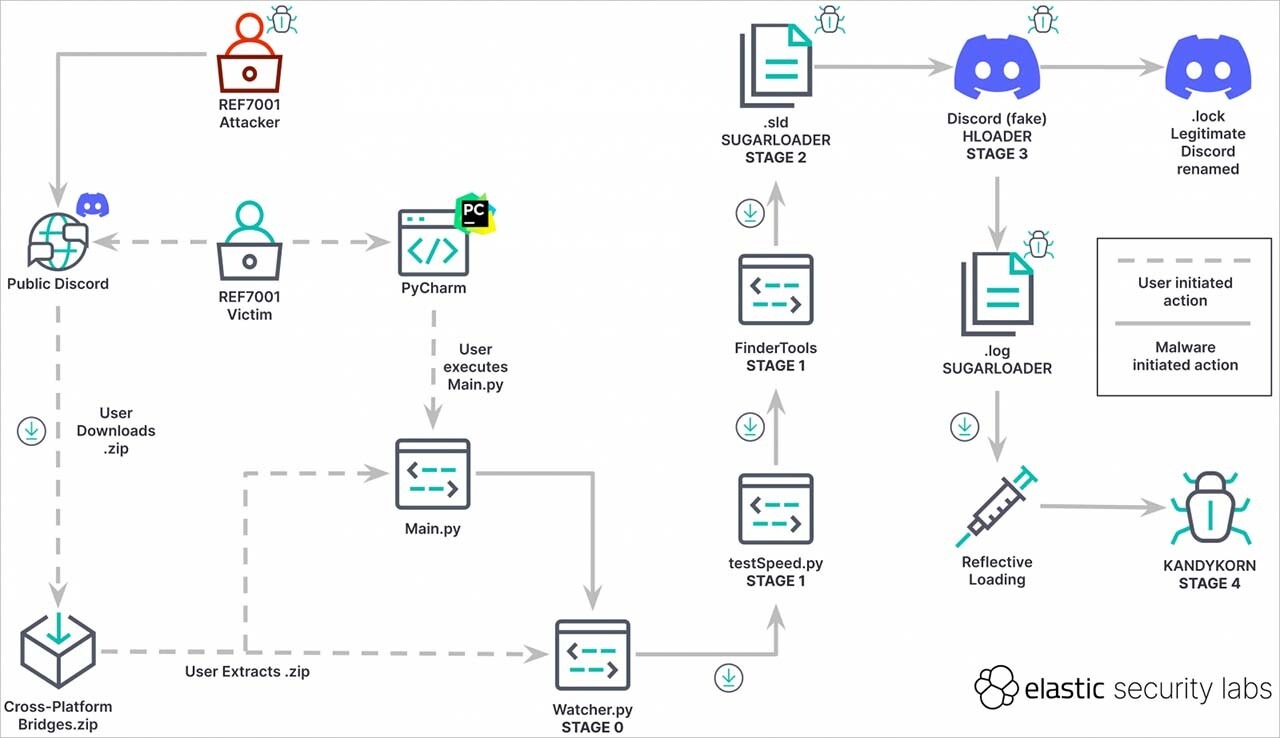
KandyKorn employs a cunning approach to propagate itself and ensnare unsuspecting victims. The attackers behind the malware resort to social engineering techniques, exploiting Discord channels by impersonating community members. They distribute Python-based modules disguised as an arbitrage bot named “Cross-platform Bridges.zip.” Ostensibly designed for automated profit generation, this malicious ZIP archive imports 13 malevolent modules that collaborate to pilfer and manipulate sensitive information.
Execution Flow Hijacking: A Novel Technique
Elastic Security Labs’ analysis of KandyKorn has revealed a previously unseen technique employed by the threat actors behind Lazarus. Termed “execution flow hijacking,” this technique enables the malware to establish persistence on macOS systems. The presence of this sophisticated method underscores Lazarus’ adaptability and emphasizes their ability to tailor inconspicuous and highly targeted malware specifically for Apple computers.
Lazarus and the Cryptocurrency Sector: A Profit-Driven Focus
While Lazarus is known for its involvement in espionage activities, the cryptocurrency sector has become a primary target due to its potential for financial gain. The North Korean hacking group is motivated by the lucrative opportunities presented by the cryptocurrency landscape. KandyKorn’s existence serves as a stark reminder that macOS is well within Lazarus’ crosshairs. Their ability to craft intricate and discreet malware tailored for Apple systems showcases the extent of their technical prowess.
Unibot Exploit: Implications for the Decentralized Exchange
In a separate incident, the popular Telegram bot, Unibot, which is utilized to conduct trades on the decentralized exchange Uniswap, fell victim to an exploit. This exploit resulted in a rapid 40% decline in the token’s price within a single hour. Blockchain analytics firm Scopescan promptly alerted Unibot users about the ongoing hack, which was later confirmed by an official source associated with the platform.
The official statement released by Unibot reassured its users and pledged to compensate those who lost funds due to the contract exploit. This commitment demonstrates the platform’s dedication to addressing security breaches and safeguarding the interests of its user base.
Conclusion
The emergence of KandyKorn, a macOS malware attributed to the North Korean hacking group Lazarus, poses a significant threat to blockchain engineers and the broader cryptocurrency community. Its stealthy nature, coupled with the adoption of novel techniques like execution flow hijacking, highlights the need for robust cybersecurity measures. By staying vigilant, adopting best practices, and partnering with reputable security experts, individuals and organizations can mitigate the risks associated with such advanced malware.





