- EtherHiding, a new cybersecurity menace, leverages Binance’s BNB Smart Chain to embed malware within blockchain smart contracts, targeting unsuspecting victims.
- Hackers prefer BNB Smart Chain due to its cost-effectiveness compared to Ethereum, making it an attractive platform for executing EtherHiding attacks.
- EtherHiding attackers adapt their tactics by altering malware payloads and evading detection, posing ongoing challenges to cybersecurity experts.
In the dynamic landscape of cybersecurity, a new and potent menace, known as “EtherHiding,” has surfaced. Despite its misleading name, EtherHiding has minimal connections to the Ethereum blockchain. This cunning attack vector empowers malevolent actors to insidiously embed malicious code within blockchain smart contracts, with the ultimate goal of distributing malware to unsuspecting victims.
The emergence of EtherHiding was first brought to light by CoinTelegraph on October 16. This revelation has provided valuable insights into the tactics employed by cybercriminals and the reasons behind their choice of EtherHiding. To comprehend the allure of this threat and its complex intricacies, we delve deeper into its modus operandi.
The Allure of Binance’s BNB Smart Chain
What sets EtherHiding apart from conventional threats is the preference of its perpetrators for Binance’s BNB Smart Chain over other blockchain platforms. This preference is chiefly motivated by the cost-effectiveness of BNB Smart Chain in contrast to Ethereum (ETH). Joe Green, a security researcher at CertiK, a prominent blockchain security firm, elucidates, “The handling fee of BSC is significantly lower than that of ETH. Remarkably, this cost efficiency does not compromise the network’s stability or speed. Each update of the JavaScript Payload is remarkably budget-friendly, relieving any financial constraints.”
Unveiling the EtherHiding Assault
EtherHiding attacks typically originate from hackers infiltrating WordPress websites, where they surreptitiously inject code designed to extract partial payloads concealed within Binance’s smart contracts. Once inside, the hackers replace the website’s front-end with a deceptive browser update prompt. When unsuspecting users click on this fraudulent prompt, it triggers the extraction of the JavaScript payload from the Binance blockchain.
Evasive Maneuvers and Constant Evolution
What makes EtherHiding particularly menacing is the attackers’ adaptability. They consistently alter their malware payloads and update website domains to elude detection. This shrewd strategy enables them to perpetually present users with seemingly innocuous browser updates, all the while concealing harmful malware downloads. These deceptive tactics pose significant challenges to cybersecurity experts striving to combat EtherHiding.
Ethereum’s Increased Scrutiny
While the reasons behind the choice of BNB Smart Chain over other blockchains for EtherHiding remain somewhat enigmatic, it is postulated that heightened security-related scrutiny on Ethereum may play a pivotal role. This enhanced scrutiny stems from systems such as Infura’s IP address tracking for MetaMask transactions, which could expose hackers and elevate the risk of detection.
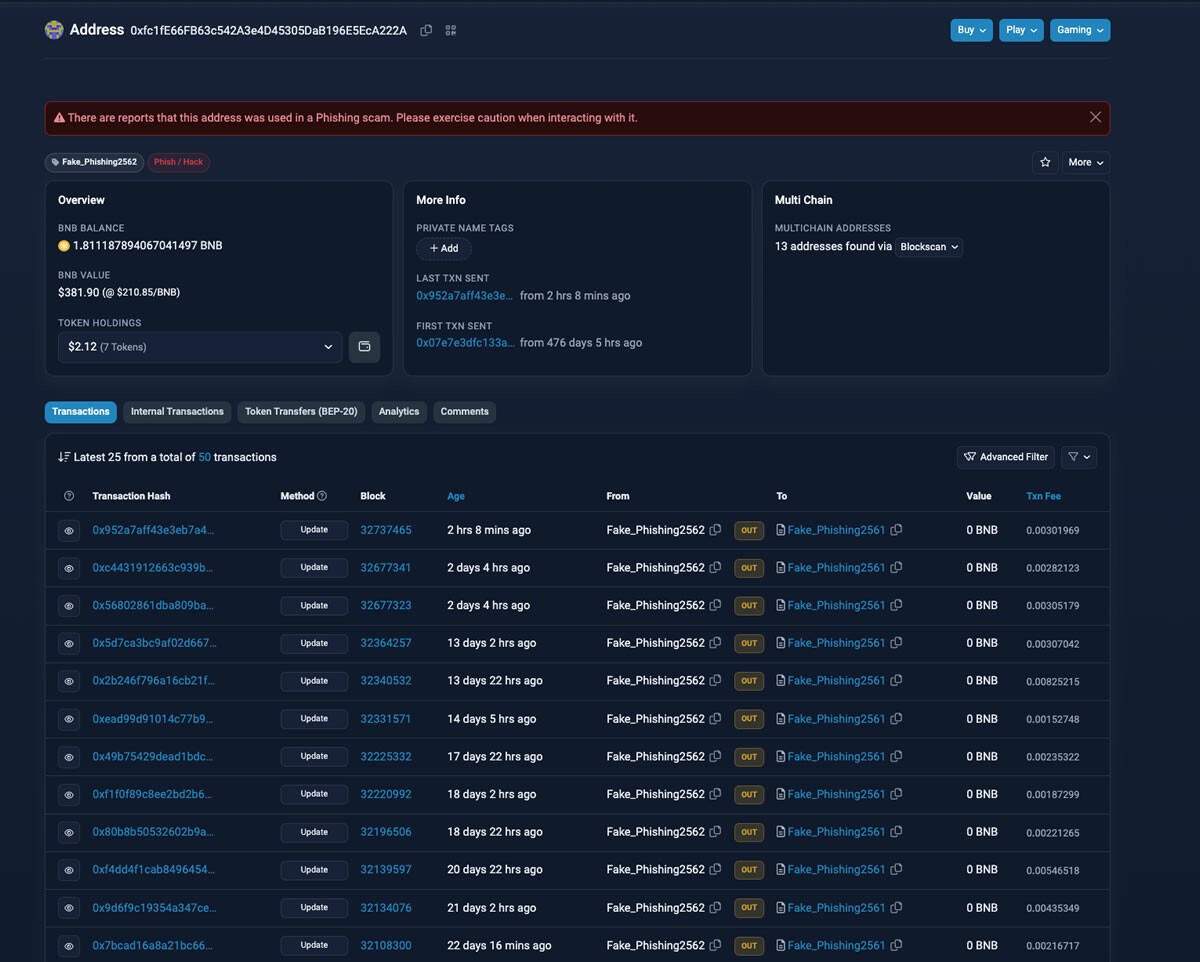
The Money Trail and Cyber Connections
Recent investigations by the 0xScope team have unveiled the complex web of financial transactions between hacker addresses on both BNB Smart Chain and Ethereum. Significantly, key addresses have been found to be linked to users of the NFT marketplace OpenSea and Copper custody services, underscoring the interconnectedness of the digital realm.
The Ever-Evolving Threat
EtherHiding attackers consistently update payloads across 18 distinct domains, making detection and prevention exceedingly challenging. Their highly sophisticated tactics continue to evolve, posing a persistent and ever-present threat to the cybersecurity landscape.
Conclusion
In conclusion, EtherHiding represents a novel and highly adaptive threat in the world of blockchain and cybersecurity. As malicious actors exploit the unique attributes of Binance’s BNB Smart Chain and continuously refine their tactics, the battle against this insidious threat continues. Vigilance and a comprehensive understanding of these evolving attacks are essential in safeguarding the digital realm.
Disclaimer
The information provided in this article is for informational purposes only and should not be considered financial advice. The article does not offer sufficient information to make investment decisions, nor does it constitute an offer, recommendation, or solicitation to buy or sell any financial instrument. The content is opinion of the author and does not reflect any view or suggestion or any kind of advise from CryptoNewsBytes.com. The author declares he does not hold any of the above mentioned tokens or received any incentive from any company.
image source





