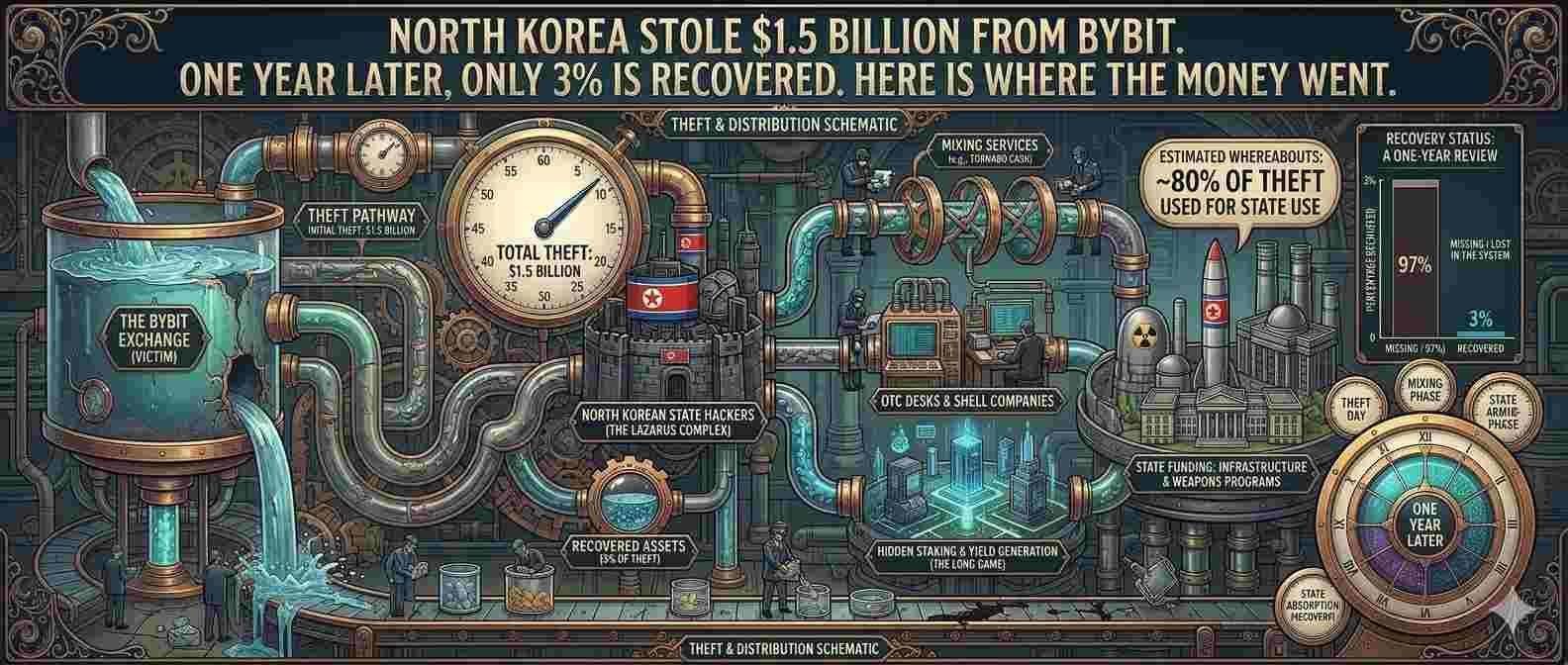
On February 21, 2025, 401,347 Ethereum tokens worth approximately $1.5 billion disappeared from Bybit in under two minutes. It remains the largest theft in the history of cryptocurrency, surpassing every bank heist ever recorded including the $1 billion Saddam Hussein took from Iraq’s central bank in 2003. The FBI confirmed North Korea’s Lazarus Group as the perpetrators within five days. More than a year later, less than 3 percent of the stolen funds have been recovered. The rest is either still moving through blockchain laundering infrastructure or has gone permanently dark.
What makes the Bybit hack worth examining now, in 2026, is not the mechanics of how it happened. Those have been documented extensively. What matters is what the money trail reveals about where North Korea’s cyber programme has gone since the theft. Chainalysis data shows North Korean groups stole $2.02 billion across all operations in 2025. Bybit alone accounted for 76 percent of every dollar stolen from crypto exchanges that year. The DPRK’s total crypto theft since 2017 now stands at $6.75 billion. These are not criminal proceeds. They are weapons programme revenues, and the Bybit operation was, by that measure, the single most profitable weapons financing event in North Korean history.
| $1.5B Stolen Feb 21, 2025, Largest Crypto Heist Ever | <3% Recovered as of Feb 2026 Anniversary | $6.75B DPRK Total Crypto Theft Since 2017 |
How North Korea Did It: The Supply Chain Attack Nobody Saw Coming
The Bybit hack did not start at Bybit. It started months earlier, at a third-party software company called Safe, the multisignature wallet platform that Bybit used to manage its cold storage. North Korean hackers operating under the FBI designation TraderTraitor, a subunit of the DPRK’s RGB 3rd Bureau, identified a developer at Safe who had system administrator privileges. Through a combination of phishing and social engineering, consistent with North Korea’s documented Contagious Interview campaign, they compromised that developer’s laptop and hijacked their AWS session tokens to bypass multi-factor authentication controls.
On February 19, 2025, with access to Safe’s frontend delivery infrastructure, the attackers injected malicious JavaScript into Safe’s web interface. The code was surgical. It activated only when Bybit specifically opened its Safe account and only during a transaction from its Ethereum cold wallet. Every other Safe user on the planet continued using the interface normally. Bybit’s own employees saw a completely normal transfer screen when they reviewed the transaction. What they were actually signing, invisibly beneath the interface, was a delegatecall command that handed control of Bybit’s cold wallet smart contract to an attacker-controlled address. Three signatures were collected. The transaction executed. In under two minutes, 401,347 ETH was gone.
Forensic investigations by Sygnia and Verichains, both commissioned by Bybit, confirmed the root cause: malicious code originating from Safe’s infrastructure, deployed February 19, activating February 21. Safe’s own investigation, conducted with cybersecurity firm Mandiant, confirmed the developer’s machine was the entry point. Mandiant is the firm Google acquired for $5.4 billion. (TRM Labs, February 27, 2025)
Where the $1.5 Billion Went: Status as of March 2026
Source: Bybit LazarusBounty programme, Chainalysis, TRM Labs, AGBI | March 2026.
| Gone Dark (unrecoverable) | $1B+ | |
| In Laundering Channels | ~$400M | |
| Still Traceable | ~$141M | |
| Frozen | $73M | |
| Recovered | <$30M |
Bybit’s LazarusBounty programme has paid $2.3 million to 13 bounty hunters as of late 2025. Over 5,000 reports were submitted; only 63 were deemed valid. The window for recovery narrows every month as funds move deeper into laundering networks.
The Laundering Operation: Faster Than Any Compliance Team Could Track
The speed of what followed the theft was as remarkable as the theft itself. Within 48 hours, at least $160 million had been funnelled through illicit channels. By February 26, over $400 million had been moved and partially converted. The playbook is now well-documented by TRM Labs and Chainalysis: the stolen ETH was split across 50 wallets each holding roughly 10,000 ETH, pushed through decentralised exchanges to convert into other tokens without triggering KYC checks, moved across blockchain networks using cross-chain bridges to create forensic complexity, and ultimately converted into Bitcoin, which is structurally harder to trace than Ethereum due to the UTXO transaction model.
One exchange, eXch, became a notable problem. Despite Bybit’s explicit requests to freeze assets, eXch permitted swaps of the flagged funds, generating hundreds of thousands of dollars in fees from the process. CSIS documented this as illustrating a core weakness in the current regulatory structure: there are few incentives for smaller exchanges operating in permissive jurisdictions to refuse business from high-volume sources, even flagged ones.
The FBI released 51 Ethereum addresses linked to the laundering operation and issued a public service announcement urging cryptocurrency providers to block transactions from those addresses. OFAC added numerous Lazarus-associated wallet addresses to its sanctions list. Neither action meaningfully slowed the money flow. By the time coordinated exchange blacklisting could be implemented, the funds had already moved downstream.
This Was Not a Hack. It Was a Weapons Financing Operation.
The Bybit theft needs to be understood in its strategic context rather than solely as a cybersecurity incident. A senior Biden administration official stated that approximately 50 percent of North Korea’s foreign currency earnings come from cybercrime. The Chainalysis 2026 Crypto Crime Report confirms that North Korean-linked groups stole $2.02 billion in 2025, a 51 percent increase year over year. Total DPRK crypto theft since 2017 now stands at $6.75 billion. These funds, according to US government assessments, flow directly into North Korea’s ballistic missile and nuclear weapons programmes, helping Pyongyang evade international sanctions that have largely shut it out of the traditional banking system.
Bybit alone, at $1.5 billion, represented more than all of North Korea’s 2023 crypto theft operations combined. The regime stole $660 million across 20 incidents in 2023 and $1.34 billion across 47 incidents in 2024. With a single operation, in a single day, it exceeded all of 2023 by a factor of two. That is not opportunistic cybercrime. That is a sophisticated state-level financial operation with a specific strategic objective.
What Chainalysis describes as the evolution of DPRK tactics in 2026 is alarming in a different way. Post-Bybit, North Korean hackers are increasingly targeting the infrastructure beneath exchanges, the wallet providers, key management systems, and bridge protocols, rather than exchanges directly. TRM Labs’ Nick Carlsen, a former FBI subject matter expert, describes a “flood the zone” strategy, overwhelming compliance teams and blockchain analysts with high-frequency transactions across multiple platforms simultaneously, making coordinated tracking practically impossible. The Tenexium incident in early 2026, the first confirmed North Korea-linked hack of 2026, is believed to have involved insider access obtained through a fake recruitment process conducted on LinkedIn. (Chainalysis 2026 Crypto Crime Report)
Bybit’s Response: What the Exchange Did Right and What the Industry Still Has Not Fixed
Bybit’s crisis response is genuinely worth studying. CEO Ben Zhou provided transparent public updates throughout, including a post disclosing that Bybit had received warnings about compatibility issues with Safe months before the breach but had not acted on them. The exchange secured emergency liquidity from Galaxy Digital, FalconX, and Wintermute within hours, covering the 447,000 ETH deficit and keeping withdrawals fully operational within 72 hours. A proof of reserves audit by Hacken confirmed all major assets exceeded 100 percent collateralisation shortly after. The LazarusBounty programme, offering 10 percent of recovered funds, attracted over 5,000 submissions, paid $2.3 million to 13 bounty hunters, and helped freeze $73 million. Bybit underwent more than 30 external security audits in the aftermath and rebuilt core wallet infrastructure. It grew from 50 million to 80 million registered users despite the incident, a counterintuitive result that reflects how the transparent response maintained trust.
What the industry still has not fixed is the underlying structural problem the Bybit hack exposed. The attack surface was not Bybit’s own infrastructure. It was the web of third-party software providers, wallet platforms, key management services, and bridge protocols that exchanges rely on without being able to fully audit. Bybit’s cold wallet itself was never compromised. The blockchain worked exactly as designed. The compromise happened in the human-facing software layer above it, specifically in a UI that showed signers a legitimate transaction while they were actually authorising a malicious one. The term for what Bybit’s signers did is blind signing, approving a transaction based on what the interface displays rather than verifying the underlying raw transaction data. Clear signing, where a hardware security module displays the actual transaction parameters rather than the UI’s interpretation of them, would have caught this attack. Widespread adoption of that standard across the industry has not yet happened.
For our coverage of how state-sponsored social engineering attacks connect to the broader 2026 crypto crime landscape, see the cyber insurance deep dive and the DAO governance attack explainer. For the regulatory framework the Bybit incident helped accelerate, see our coverage of the SEC-CFTC joint framework and OCC digital asset custody rules.
FAQs: The Bybit Hack and North Korea’s Crypto War Machine
Related Coverage on CryptoNewsBytes
The Bybit hack is the defining case study for why crypto-specific cyber insurance is structurally different from traditional coverage. What a $1.5 billion supply chain loss means for policy language and exclusions.
The economic exploit that sits alongside supply chain attacks as the dominant crypto threat model in 2026. Different mechanism, same lesson: the blockchain works as designed, and the attack happens in the layer around it.
The regulatory framework that the Bybit hack helped accelerate. State-sponsored crypto theft on this scale drove regulatory urgency in a way that smaller incidents had not.
DeFi’s economic exploit problem alongside the exchange supply chain problem. The attack surface in 2026 extends across every layer of the crypto stack.
The other defining financial crime case in crypto: not a hack but alleged market manipulation. Two different threat models, one consistent pattern of inadequate institutional safeguards.
The institutional adoption story happening simultaneously with the security threat story. Wall Street building Bitcoin infrastructure while North Korea weaponises it.
Primary sources: Chainalysis 2026 Crypto Crime Report | TRM Labs | FBI TraderTraitor attribution, February 26, 2025 | CSIS analysis | Bybit LazarusBounty programme data | Mandiant/Safe investigation report | AGBI, September 2025. This article is for informational purposes only and does not constitute financial or investment advice.